In this tutorial, I will be discussing when you should or shouldn’t apply automatic security updates on CentOS. Once complete I’ll guide you on how to set up automatic security updates and exclude certain packages.
If you’ve already decided that you would like to set up automatic updates, you can scroll down to the installing and configuring automatic updates on CentOS section.
When to apply Automatic Security Updates?
For some, such as the general computer user, automatic security updates are a great feature. They allow you to stay on top of Cybersecurity threats. However, for others, such as System Administrators, they can be the bane of existence.
Personally, I choose to opt-in to Automatic Security updates for personal use and opt-out in my Server Administration life.
Below is a list of some of the benefits and downsides to Automatic Security Updates.
Benefits – Automatic Security Updates
- Cybersecurity is a growing concern and automatic security updates keep you on top of real-world threats.
- Increased user experience, you no longer need to worry about manually checking for updates.
Downside – Automatic Security Updates
- Security updates can cause issues with network packages.
- You don’t always know what’s being installed.
- Uses internet bandwidth you may not have.
Installing and configuring Automatic Security Updates using Yum-Cron on CentOS
In order to setup Automatic Security Updates, we will need to install and configure Yum-Cron. Yum-Cron is a Yum module that allows you to configure an automated task(Cron jobs) specifically for the Yum package manager.
To install yum-cron type the below command into the terminal:
sudo yum install yum-cron
Once Yum-cron is installed, the below message will be displayed.
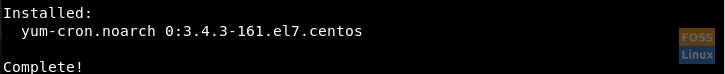
Yum-Cron installation confirmation.
You will now be able to configure Yum-Cron using your chosen text editor, throughout this tutorial I’ll be using Nano. Type the below command to open the Yum-Cron configuration file with Nano.
sudo nano /etc/yum/yum-cron.conf
You will be welcomed with the following file. If you’re new to Linux, this may be a bit daunting, but don’t worry, I will guide you through what to change.
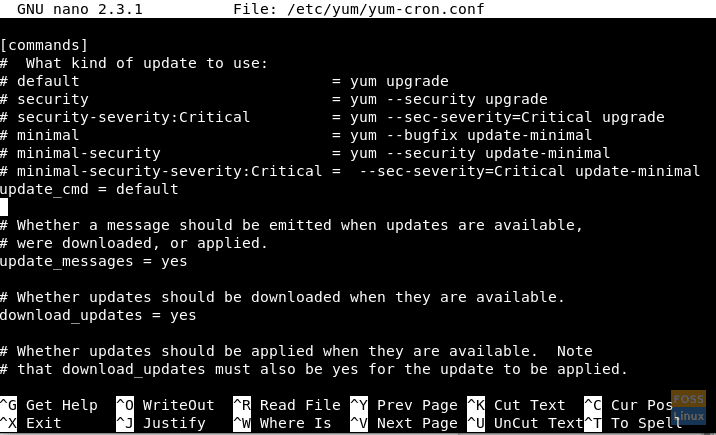
yum-cron configuration file.
Change the value of the ‘update_cmd’ property from ‘default’ to ‘security’, as per below example.
update_cmd = security
If you don’t want to be warned about an update before it takes place, you’ll also need to change the value of the below line from ‘yes’ to ‘no’.
update_messages = yes
Now you’ll need to make sure that Yum-Cron is configured to download updates, make sure the value of the below line is ‘yes’.
download_updates = yes
Lastly, you will need to make sure that Yum-Cron is configured to install the updates, make sure the value of the below line is ‘yes’.
apply_updates = yes
Now use {Ctrl+X} to exit out of the Yum-Cron configuration file. You will be asked whether you would like to save, tap ‘y’, followed by the ‘enter’ key to overwrite the default configuration file.
Exclude packages from Automatically Updating
In this section of the tutorial, I am going to guide you on how to exclude certain software packages from Automatically downloading security updates.
If you want to exclude a particular package you will first need to know the full name of that package. If however, you would like to exclude a group of packages, such as any package with PHP in the title you can use the ‘*’(Wildcard) symbol.
If you don’t know the full name of the package you want to exclude, run the following command to list all currently installed packages and look for the particular package/s that you would like to exclude.
yum list installed
If there are multiple packages to exclude, I would recommend snapping 2 terminal sessions side by side for reference, as per below screenshot.
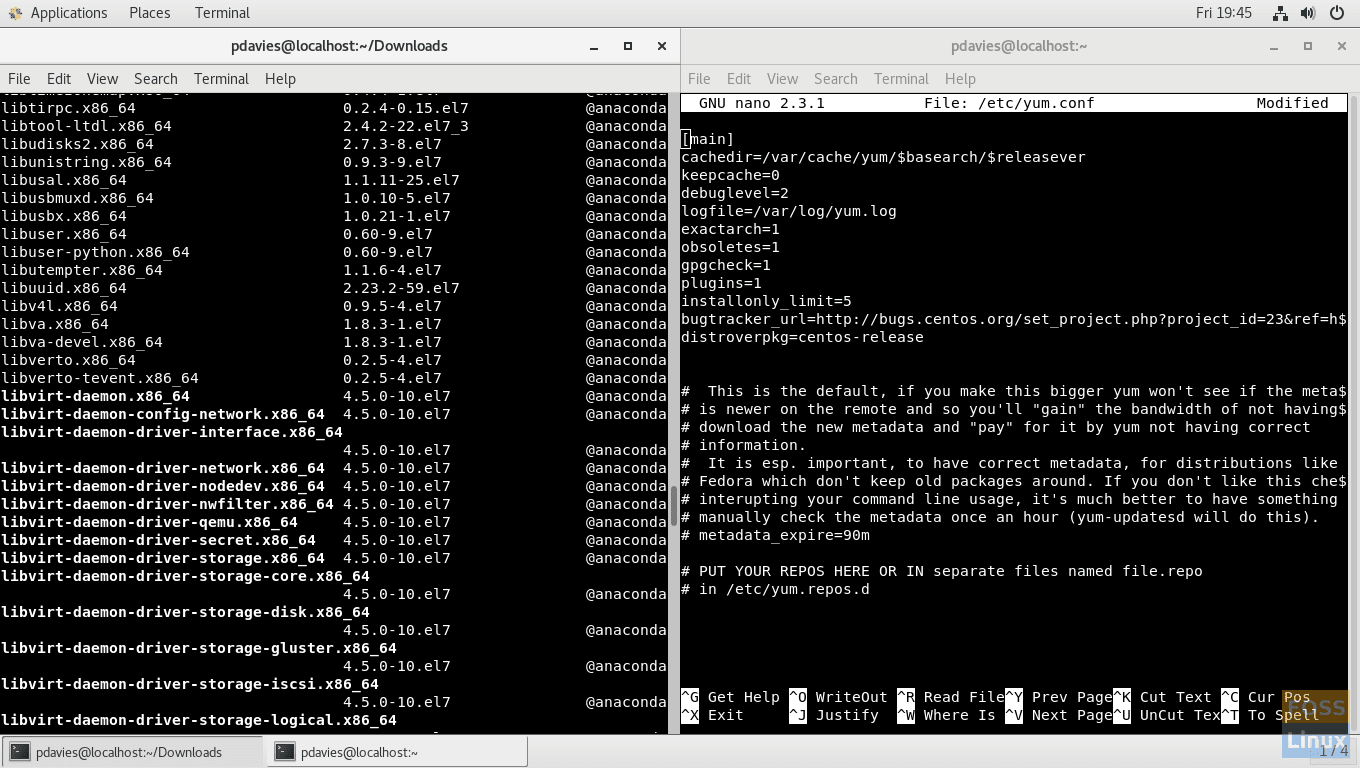
Snapping windows.
Run the below command to open the yum configuration file.
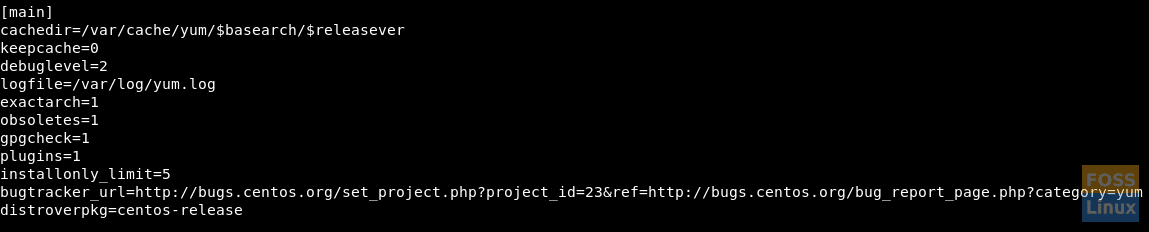
sudo nano /etc/yum.conf
You will be welcomed with the below configuration file. Move the text cursor to the bottom of this section of code.
Add the following line to the configuration file.
exclude=
Type the packages separated by spaces as the value to the ‘exclude=’ property using the below example as a guide. If you want to exclude multiple related packages, you may be able to do them in batch by using the wildcard ‘*’ symbol. In the below example I am excluding all packages that have ‘libre’ anywhere in the title along with brasero.x86_64.
exclude=*libre* brasero.x86_64
Press {Ctrl + x} and save the configuration file.
Now you’re ready to start the yum-cron service. To do this, type the below command.
service yum-cron start
If successful the below message will be returned.
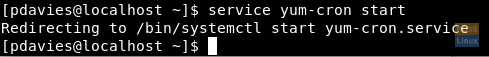
Starting the yum-cron service.
Now Yum-Cron is configured to perform weekly checks for Security Updates and will download/ install them automatically.

2 comments
Please check centos.org Forums. There is numerous mentioning that the CentOS repository does not include the needed flag about a package being a security patch, only the RedHat repos. Thus, the abovementioned commands will work on CentOS without errors, but will never update anything, giving the administrator a false sense of security. That’s even worse than knowing that your system is insecure.
This is a really helpful tutorial.