One of the significant entities we have in Cyber Security is Ethical Hacking (ETH). It is the process of detecting and finding flaws or vulnerabilities in a system that a hacker would exploit.
Anyone performing penetration testing would need several requirements to find the vulnerabilities and flaws in a system. One of them is an operating system dedicated to doing such tasks, e.g., Kali, Parrot, etc. You will also need several penetration tools and scripts. Even though these resources seem to be pretty efficient, background knowledge of different programming languages has proven to be essential in Ethical hacking.
Why are different programming languages an essential resource for an ethical hacker?
Target System Working nature
One main reason is that before carrying out any exploit, you need to understand the working of the target system or application.
For example, if the victim is a web system developed with PHP, Javascript, and Html, prior knowledge of the three would be excellent since you will know what exactly to look for and type of exploits to execute.
Scripting
Another reason is that you will be able to write your scripts or malware, which you will use on the victim. Even though there are scripts out there that perform extraordinary attacks, you might need to apply your skills in case the script doesn’t meet your requirements.
Modifying Scripts
The last main reason is that some of these scripts need some modification before using them. Therefore, if you get a script written in Python and you have never worked with Python before, this will be a significant hindrance for you. Keep in mind, “Time is of great essence in hacking.”
The Best Programming Languages for Hacking
With that in mind, let’s look at the ten best Programming Languages for Hacking. Before diving into this, it would be great to note that your programming of choice will much depend on the type of system you are targeting and the exploits you plan to use. Therefore, any language would be great, depending on your strategy.
1. Python
It’s no surprise that Python tops our list. Referred to as the defacto hacking programing language, Python has indeed played a significant role in the writing of hacking scripts, exploits, and malicious programs.

Python is a general-purpose programming language used in several development areas, including GUI, Web, and even Network programming. The latter is one that plays a crucial role in writing hacking scripts. One unique feature with Python is the simplicity in syntax.
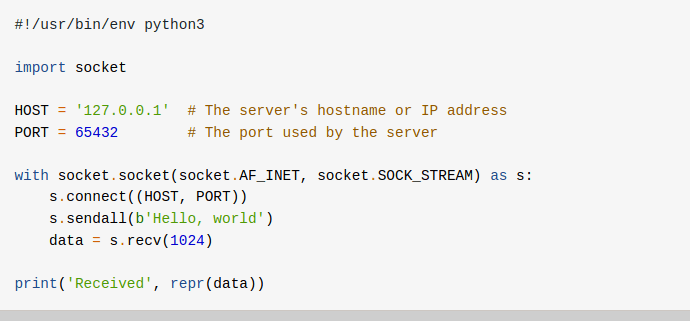
Python Socket Programming code
Another feature that makes hacking with Python amazing is the availability of ready-made modules – lots of them. If you want to target the native operating system, we have the OS modules. If you are working with IP-addresses, we have the IP-address module; for networking, we have the socket module, scrapping modules, and a lot more. If you are a newbie getting started with hacking, consider Python at the top of your list.
2. C Programming
Coined as the “Mother of all programming languages,” is also a critical language in the Hacking community. Most of the popular operating systems we have today run on a foundation of C language. From Windows, Unix kernel to Linux and its distributions.

The low-level nature of C programming gives it an added advantage over most languages. It has enabled hackers and security personnel to manipulate system resources and hardware, including RAM.
C is known for writing extremely faster exploits that execute at a lower level of the system. C programming is also known for getting access to resources like memory and system processes after performing an attack and compromising a system.
C programming is an excellent resource in reverse engineering of software and applications. These enable hackers to understand the working of a system or an app.
3. SQL
SQL – Standard Query Language. It is a programming language used to organize, add, retrieve, remove, or edit data in a database. A lot of systems store their data in databases such as MySQL, MS SQL, and PostgreSQL.
Using SQL, hackers can perform an attack known as SQL injection, which will enable them to access confidential information.

Also, having excellent skills with SQL lets you understand the structure of a database and how it works. Such information will simplify your work as you will know which exact scripts/tools to deploy.
4. Javascript
For quite some time, Javascript(JS) was a client-side scripting language. With the release of Node.js, Javascript now supports backend development posing stiff competition to PHP. To hackers, this means a broader field of exploitation.

Understanding Javascript gives you a higher privilege in Web exploitation since barely all-powerful web apps use Javascript or one of its libraries.
Javascript is commonly known for carrying out attacks like cross-site scripting. Also, powerful hacking tools like Burp Suite much rely on Javascript to perform exploitation.
5. PHP
PHP stands for PHP Hypertext PreProcessor. For a long time now, PHP has dominated the backend of most websites and web applications. Even popular Content Management Systems(CMS) like Wordpress and Drupal run on a foundation of PHP.

If you are into web hacking, then getting your hands on PHP would be of great advantage. With upgrades recent upgrades to PHP 7.4.5, we still have websites on the older versions. With excellent skills, you would be able to exploit these deprecated libraries on most Web apps.
6. C++ Programming
Have you ever thought of cracking corporate(paid) software? Here is your answer. The hacker community has significantly implemented this language to remove trial periods on paid software and even the operating system.
Just like the C programming language, C++ gives you low-level access to system resources and analyzes the machine code of such software. You can then bypass the activation scheme embedded in these applications.
Even lots of reverse engineering tools we have in hacking Linux distros used C++ to perform such tasks. Therefore, if you are into exploiting Desktop software and doing reverse engineering, C++ would be of great advantage.
7. JAVA
Currently, Java is one of the most widely used programming languages used in system and mobile development. The slogan “write once, run everywhere” is used to show its cross-platform capabilities. It also powers a good number of webservers like Apache Tomcat and Spring MVC.
Despite what many may say, a lot of backdoor exploits in systems are written in Java. It has also been used by hackers to perform identity thefts, create botnets, and even perform malicious activities on the client system undetected.
Have you ever wondered how people could hack into your phone and read confidential information like messages, contacts, call logs, send messages via your phone, etc. ? Most of these are Java payloads installed into victims’ phones through social engineering.
However, if you want to use Java for hacking, you will need to dedicate your time and get a good understanding of the language as most newbies find it overwhelming compared to C and C++.
8. RUBY
Ruby has been used for exploitation fro quite a long time now. It has a similar syntax to Python, but it’s more web-oriented. Ruby can be used to write small or large scripts and can be used interchangeably with Bash scripting.
One of the popular hacking tools we have – The Metasploit penetration testing framework, is founded on Ruby.
9. Perl
Even though Perl has lost the fame it once held due to the rise of languages like Perl and Ruby, it still holds a functional space in the hacker community. We also have systems that still run on Perl.
The extensibility of this language makes it an excellent utility for hackers to create tools and exploits. It’s also the best programming language to use in manipulating Linux text files. Perl can also be used to exploit web- databases since it comes integrated into most of them
10. Bash
Even though there are still debates about whether Bash is a fully-fledged programming language? It couldn’t miss on this list. Bash is the default command shell for Unix and all Linux distributions. Keep in mind that Linux powers most servers on the internet.

Bash can be used with other programming languages like Python to enhance the functionality of your payloads or exploits. For example, you could write a Python code that wraps a Bash script. Once the Python code is run on a victim’s computer, it executes the Bash script automatically.
Once you have gained access to a system, you will need to navigate through the different directories and even perform configurations to elevate your privileges on the network. You will require Bash knowledge.
Conclusion
If you want to become a professional, ethical hacker, you shouldn’t limit yourself to programming languages. Hacking is more of an art than a course. You need to have a good understanding of computer technology from networking, databases, etc. That is because different systems require different attack vectors and exploits.
I hope this article has given you insight into what different programming languages offer, and you can decide which suits your hacking niche or attack you want to carry out.

7 comments
hi there, your site is amazing.Following your news.
Samee
Same
It’s really helpful for me
Verry useful information
Thanks for the info I really was touched
At present we are not secure on any online platform. Hackers play with your information all the time. They can hack anyone’s information at any moment. So we should make all kinds of accounts more secure. There is nothing wrong with learning moral hacking. Ethical hacking needs to be learned in order to make online business more secure nowadays.
I have every reason to do what I had to do if you were in my shoes! I couldn’t take it any longer. I had spent over a thousand dollars on medication she couldn’t stop. he was a drug addict i realized a bit late through his text messages and recent call records to different hard drug dealers. he had gotten to the point of selling them for a living and i noticed he is always spending lavishly and never thought of our kids and I thought that was enough until he brought a woman to our bed while i was away to satisfy his sexual urge. I got all the information I needed from him through the great services of FR ED VA L CY BER GHO ST @ GM AIL. C OM and you can text, call him on +–1— (4==2==3)==6==41== 1==4==5==2 and whatsapp him on +19782951763 I won’t have known if i didn’t take this good step. I ended it when we got to court with the concrete evidence I got!. I am happy to live a life without his unnecessary acts