Kali Linux is the most popular operating system for security professionals because it comes equipped with all the popular penetration-testing tools, reducing installation costs. Also, Kali Linux is a Linux-based operating system making it less prone to virus attacks while, on the other hand, providing more stability during the penetration and testing period.
Therefore, Kali Linux will save you the time needed to install the necessary and relevant tools and components, plus the stress of plunging into errors during the installation period.
Metasploit is a re-known penetration testing platform that allows the user to exploit, find and validate vulnerabilities. Therefore, it is vital to provide the tools, content, and infrastructure required to perform penetration tests and extensive security auditing.
New Metasploit modules are provided regularly thanks to Rapid7’s open-source community’s hard work and dedication, ensuring users are always updated with the latest releases. As a result, the Metasploit framework is considered the most helpful security auditing tool freely available to security professionals today.
Metasploit consists of a data store and modules in which you can configure the aspects within the framework. The modules are self-contained snippets of codes from which Metasploit derives its features. When you install and set up Metasploit on your PC, it includes a full suite of post-exploitation tools.
These tools include: privilege escalation, pass the hash, packet sniffing, screen capture, key-loggers, and pivoting tools. You can also set up a persistent backdoor in case your machine needs a reboot.
To use Metasploit, you will need to have proficiency knowledge on:
- Kali Linux OS
- Network protocols
- vulnerability management systems
- Basic pen-testing concepts
Modules of Metasploit
Metasploit modules are the main components of Metasploit, and they are pieces of code within the database. Metasploit modules are three and are embedded in various categories as follows:
Exploits
Attackers use the codes to gain access to a vulnerable system. The attacker will attempt to leverage a vulnerability on the local system compromising the payload module such as the meterpreter shell.
Payloads
Hackers use payloads as simple scripts to interact with the hacked system. This helps them to transfer data into a victim’s system.
Auxiliaries
These modules are used for tasks like scanning in Metasploit. These types of modules do not require the use of a payload to run like exploit modules. Hence, they include valuable programs such as scanners, fuzzier, and SQL injection tools.
How to install Metasploit on Kali Linux
Since Metasploit is one of the most commonly used penetration testing tools, it comes built-in Kali Linux. If you are using Kali Linux 2.0, the Metasploit framework is already preinstalled and updated monthly.
Disable antivirus software since it detects the Metasploit framework as malicious and may cause problems with the installation and runtime of the Metasploit framework. The Metasploit framework exploits the same vulnerabilities that the antivirus detects. Hence, when installing the Metasploit framework, the antivirus software interrupts the installation process and alerts you of the security risks that may affect the system.
If you can’t disable the antivirus software, you must exclude the Metasploit directory from the scan.
Note: Remember to disable the local firewalls before installing or running the Metasploit framework. The firewall may detect the Metasploit framework as malware and interrupt the download. If you have to operate from behind a firewall, you should download the Metasploit framework from outside the network.
Metasploit installation on Kali Linux using Rapid7
Rapid7 provides an open-source installer for the Metasploit framework on the Linux Operating system. These installers include dependencies (ruby and PostgreSQL) that integrate with your package manager, making them easy to update.
The easiest way to get the Metasploit framework is by downloading the installer from the Rapid7 site. First, visit the website to find and download the installer for your operating system.
The installer provides a self-contained environment for you to run and update the Metasploit framework. All the necessary dependencies are installed and configured for you during the installation process.
When you launch the installer file, the installer will prompt you to enter the destination folder on the hard drive or external disk to install the Metasploit framework.
Install Metasploit on Kali Linux using Terminal
To install the Metasploit on Kali Linux, execute the command below:
sudo apt install metasploit-framework
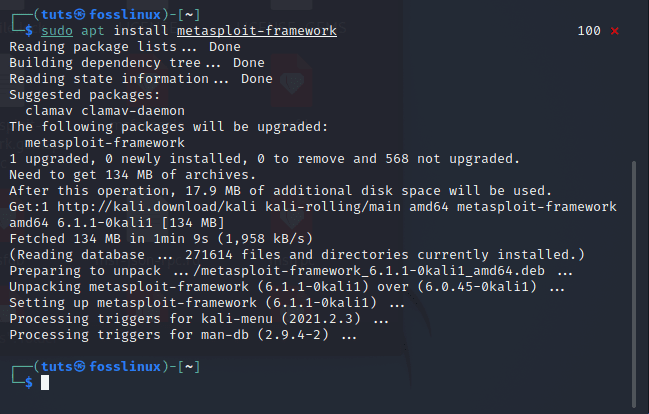
install Metasploit framework
Starting the Kali PostgreSQL service
If PostgreSQL isn’t running, use the following command to run it:
sudo /etc/init.d/postgresql start
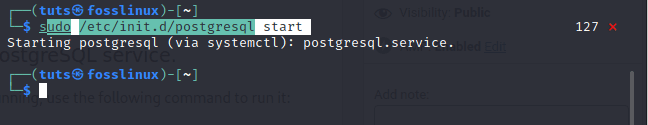
start PostgreSQL
sudo /etc/init.d/postgresql status
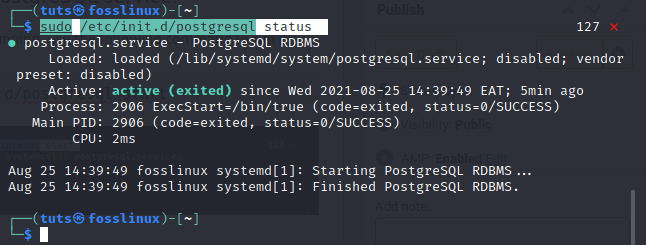
PostgreSQL status
Rapid7 includes msfconcsole and installs associated tools like Nmap and John the ripper. To install the Metasploit framework, you must have administrator privileges on the system that you want to use to run the framework.
Note: Rapid7 no longer supports the preinstalled Metasploit Community edition that is on Kali Linux 1.0.
The following script invocation will import the Rapid7 signing key and set up the package for supported Linux systems.
curl https://raw.githubusercontent.com/rapid7/metasploit-omnibus/master/config/templates/metasploit-framework-wrappers/msfupdate.erb> msfinstall && chmod 755 && msfinstall && ./msfinstall
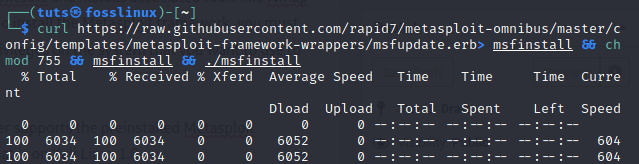
curl command
After installation is complete, open a terminal window and type the following command to start msfconsole
msfconsole -q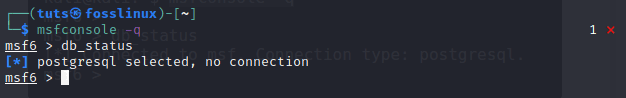
start msfconsole
Note: if you don’t have a database, you will be prompted to set up a new database.Type Y or Yes to run tyyyyhe initial configuration script to create the initial database.
It may already be in your path, and you can run it directly depending on your environment. A series of prompts will help set up a database and add Metasploit to your local path if it does not exist. These packages will integrate into your package manager and update with the msfupdate command or your package manager. The packages will automatically set up the database or use your existing database if this is the first time using it.
To check to see if the database was set up correctly, run the following command on the terminal:
db_status
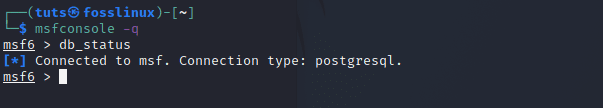
checking DB status
If the Metasploit framework is successfully connected to the database, the following status will display:
[*] Connected to msf. Connection type: postgresql.
Managing the database
In case you did not opt to create a database when msfconsole loaded for the first time, you can use the msfdb script to configure PostgreSQL to run as your local user and store the database in
Use the following command to enable and start the database:
sudo msfdb init
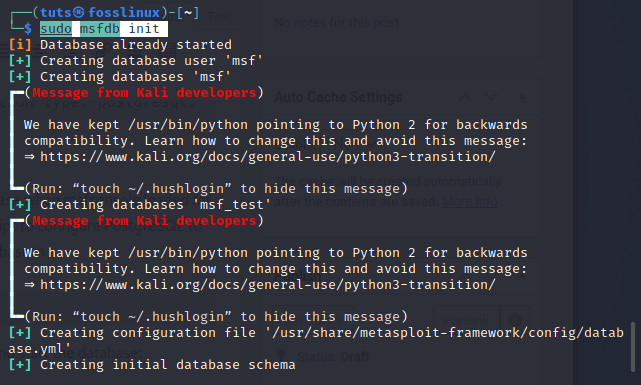
initiate mfsdb
You can use any of the following commands to manage the database:
- msfdb reinit – Deletes and re-initializes the database
- msfdb delete – Deletes the database
- msfdb start – Starts the database
- msfdb stop – Stops the database
- msfdb status – Shows the database status
- msfdb run – Starts the database and runs msfconsole
Conclusion
In this article, we have discussed Metasploit and how to install it on Kali Linux using Rapid7. We hope you find this article helpful. Feel free to use the comment section in case of any queries.
4 comments
curl https://raw.githubusercontent.com/rapid7/metasploit-omnibus/master/config/templates/metasploit-framework-wrappers/msfupdate.erb> msfinstall && chmod 755 msfinstall && ./msfinstall
you have an extra set of && after the 755
They don’t really care, they just want viewers.
curl https://raw.githubusercontent.com/rapid7/metasploit-omnibus/master/config/templates/metasploit-framework-wrappers/msfupdate.erb > msfinstall && \
chmod 755 msfinstall && \
./msfinstall
can anyojne help me in solving package not found , reach me out through mail, (sathish2002naidu@gmail.com)