A wordlist can be referred to as a password dictionary since it is a collection of passwords stored as plain text. Kali Linux is the most advanced penetration testing distribution. It is primarily designed for penetration testing and digital forensics hence funded and maintained by Offensive Security.
Most Kali Linux wordlists can be downloaded online, including those provided in this article. In addition, there are a collection of common and uncommon passwords that are still or were once used by real people. Remember, you can also create your wordlist if you prefer to or stick to the ones already compiled. Wordlists are derived from data breaches such as circumstances where the company gets hacked. Data stolen from the hacked companies are leaked on websites such as Pastebin or sold on the dark web.
If you intend to download the entire collection of wordlists, you can check them out on Github.
Note: Wordlists have been separated and sorted alphabetically to meet GitHub’s upload size minimum requirements.
Wordlists are a primary player of brute force password attacks. Newbies and readers who are not familiar with brute force attacks are an attack whereby a script is repeatedly used to attempt to log in until a positive result is attained. Then, you can choose to refer it to a trial-and-error method to get a positive unlock result. Brute force attacks are overt and can lock out an attacker from their IP whenever the server is well configured.
Testing login systems security aims to ban attackers who attempt to initiate attacks on their servers and report increased traffic. Users should also ensure their passwords are more secure to avoid being victims of rapidly increasing attackers due to technological advancements worldwide.
Note: It is vital to learn and understand how attacks are carried out to help you create and enforce a more assertive password policy.
Kali Linux Wordlist
Kali Linux comes equipped with a powerful tool used to create any length wordlists. This command is known as Crunch. It is a simple command-line utility. The tool contains a simple syntax that can be adjusted to suit the users’ needs.
Note: It is important to note that lists may be extensive. Thus, they can quickly fill your hard disk.
How to generate a list?
You do not need to install crunch since it is a tool that comes pre-installed in Kali Linux. Once you have your Kali Linux operating system powered on and ready to go, launch crunch. For a start-up, we shall create a simple list like the one displayed below:
crunch 1 3 0123456789
The above command line will create a list containing every possible combination of numbers ranging from zero to nine with an additional one, two, and three characters. To clarify, it is vital to understand that the first number should contain the smallest character combinations. For instance, in the example provided above, it is a single character password that any site should not use since it is easy to bypass or crack.
The second number contains the longest character combination. For our provided example, the number is three. So, the crunch tool will help generate a possible combination of the three provided characters.
The final part contains a list of all characters used by crunch to make the possible combinations. This list is smaller; hence, you can run it, but the list size will eventually explode as soon as you add extra or more character size. Thus, it is essential to consider the maximum combined size since it increases the overall list size, which might quickly fill your hard drive.
Though the above scenario might seem unrealistic, it might help unlock phones or some accessories of that sort. However, for more complex and realistic combinations, we shall use the syntax below:
crunch 3 5 0123456789abcdefghijklmnopqrstuvwxyz
The above command will generate possible three-, four-, and five-character combinations of numbers ranging from zero to nine and lowercase alphabet letters ranging from a to z. Although password combinations generated will be short, the lists generated will be massive.
Note: Your computer’s hardware and software resources should be up to par to run more complex combinations. For instance, for the following example, your computer should have excellent resources to try and test password security.
crunch 3 10 0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ
CAUTIONS!!! Do not run the command above. This command will generate a list of files that will fill your hard disk drive in no minute, and it renders it virtually unusable. However, the bright side about this combination is it will test every password containing three to ten characters using a combination of both upper and lowercase alphabets plus all numbers.
How to capture the wordlist output?
So far, we have been outputting numbers onto the screen, which is not very useful, considering our subject matter is wordlists. Therefore, we have to generate a text file that can be used with a different program. Crunch, a tool we had introduced earlier as a built-in utility, will help create the output in a text file.
crunch 3 5 0123456789abcdefghijklmnopqrstuvwxyz -o Documents/pass.txt
The -o flag added to the command above will create a properly formatted text file in the provided destination, which is the Documents folder.
However, there are other ways of outputting the combinations in the form of a text. For instance, a user might have a good wordlist containing popular bad passwords. In that case, they should use the default wordlist included in Kali Linux known as the rockyou.txt that can be found here /usr/share/wordlists. To save your password combinations to this text file, then you first have to decompress it.
On some occasions, the user might want to add a generated wordlist onto the already existing rockyou.txt to be in a position to provide an additional testing possibility in a single shot. If this is the case, then the user will redirect the crunch output into the file as shown below:
crunch 3 5 0123456789abcdefghijklmnopqrstuvwxyz >> /usr/share/wordlists/rockyou.txt
Before executing the command above, ensure you have enough space since the file generated will be huge to enable testing of various possibilities.
How to extract or decompress RockYou wordlist file
As already mentioned, the default or built-in Kali Linux wordlist is RockYou, and it can be found in /usr/share/wordlists. This file is compressed with Gzip. Therefore, to extract it for use, we shall follow the procedures provided below:
Step 1: Open your terminal
Step 2: Change to the RockYou directory using the command line below:
cd/usr/share/wordlists
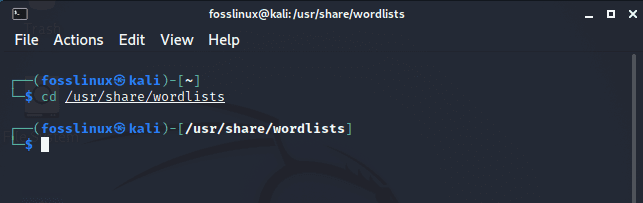
Navigate to the RockYou directory
Step 3: Use the ls command to check the RockYou file
ls
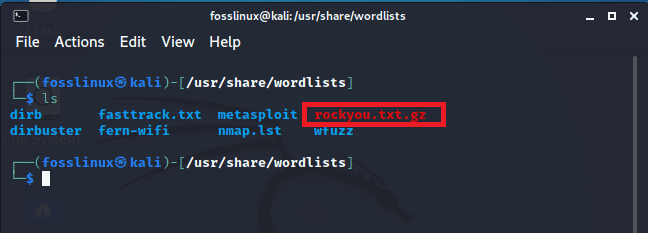
Use the ls command to check existing files in the wordlists directory
Step 4: Now, using the gunzip command, extract the file by executing the command below in the open terminal window
sudo gunzip rockyou.txt.gz
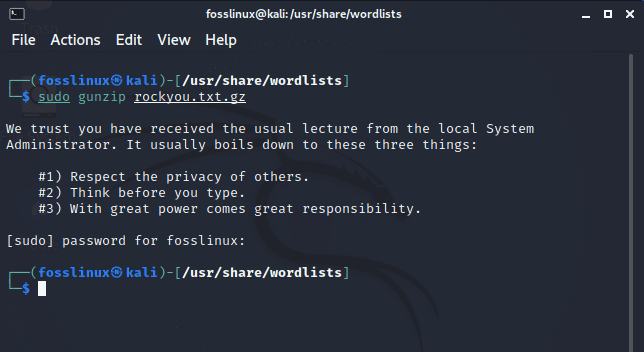
Extract the RockYou file
Note: The sudo command is used to avoid getting the “permission denied” error.
Step 5: Using the ls command, recheck to see if the initial rockyou.txt.gz file has been extracted
ls
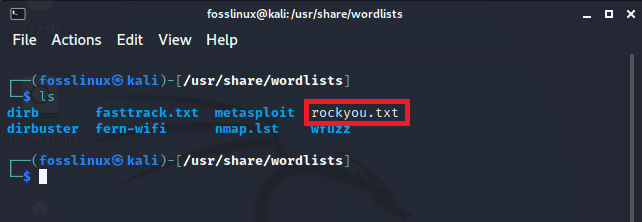
RockYou file has been successfully extracted
Note: you can download premade wordlists and password lists from here, decompress them and choose the wordlist combo you prefer to use.
Conclusion
This was a quick guide on Kali Linux wordlists. We believe the article helped you understand the concept of wordlists, how to download, create, generate and even use them. If you found the article helpful, please remember to give a thumbs up via the comments section. Thanks for reading.

