Deepin Linux is by far one of the most good-looking Linux distros out there. But as much as it’s praised for its good looks, it’s also infamous for collecting user data and sending it to Chinese servers.
So what is the truth here? Is Deepin trying to lure in users with its stunning looks and then stealing their data? Or is it just Chinese paranoia that got blown out of proportion?
In this read, we will give you an in-depth look at all the evidence and security claims surrounding Deepin OS. In addition, we will show you what started this whole “Deepin OS is Spyware” controversy and discuss the Linux distro’s current state.
So without further ado, let’s get started:
Deepin Linux’s connection to CNZZ
Deepin OS is free and open-source software. As such, any user can audit its source code to learn how it works and/or to search for security vulnerabilities. Well, that’s exactly what the YouTuber – QuidsUp did back in 2018 in his video titled “Linux Deepin is Spyware.”
Here’s the video in case you are wondering what he uncovered:
In a nutshell, QuidsUp found that in Deepin Linux 15.5, the Deepin Store was sending certain system information to a popular Chinese tracker CNZZ, the largest Chinese internet statistics analysis service provider.
What’s more alarming is that the communication was happening regardless of whether you were using the Deepin Store. According to QuidsUp, the communication was established either on system bootup or the first time you opened the Deepin Store.
So what does this mean? In layman’s terms, a third-party analytics company, that too from China, was tracking and collecting user data. And the worst part, the users were not made aware of this activity in any way.
According to QuidsUp, Deepin 15.3 and 15.4 didn’t have the CNZZ tracker. So Deepin added it in with the release of version 15.5. However, users who downloaded and installed Deepin weren’t notified of this significant change.
For reference, Ubuntu is also known to collect anonymous user data. However, they inform the user about this behavior right after installing the distro. Furthermore, Ubuntu users also have the option to opt out of all the data collection stuff.
With Deepin 15.5, neither were the users told, nor were the users given an option to opt-out!
Deepin’s response to the controversy
Shortly after QuidsUp’s video went online and other Linux outlets started talking about the findings, the Deepin team quickly responded to shed light on what was happening.
It turned out that the Deepin store backend is actually a website – which, by the way, is true for many other Linux apps as well.
The CNZZ tracker was embedded in the store’s backend to collect anonymous website usage information like “browser user agent, resolution, etc.” Now the fact that Deepin opted to use an ‘etc.’ instead of elaborating on all the metrics that were being collected is a cause for concern for many. Furthermore, the data it was sending was encrypted, making it impossible to know the kind of stuff they are collecting.
According to them, the service is “similar to Google Analytics,” implying that the type of data collected is similar to what’s collected by other websites using Google Analytics.
They have also explicitly cited that “no private information” is collected by Deepin.
As far as the reason for collecting user data, Deepin stated that by using CNZZ, they hoped to “improve website experience” and “detect website problems.”
After publishing the statement, Deepin removed the CNZZ tracker from the Deepin store. QuidsUp also made a follow-up video after the statement and concluded that Deepin has genuinely removed CNZZ tracking.
Now, all of this happened in 2018. We are in 2021, and it’s been nearly 3 years now. So, is everything okay, and is Deepin safe to use?
The current state of Deepin Linux
Deepin Linux initially started out as a community-based distribution back in 2004. Then, in 2011, the Deepin Linux development team got together and created their own company – Wuhan Deepin Linux. After that, as of January 1, 2020, Deepin Linux is a wholly-owned subsidiary of Union Tech.
Now here’s the thing, Union Tech started out as a joint venture between Wuhan Deepin Technology and a state-run corporation. And now, it has completely acquired Deepin, and the Deepin founder Liu Wenhan is placed as Union Tech’s General Manager. This means that the Chinese government now has even more power over Deepin OS as it’s owned by a state-run corporation.
On the surface, this does appear scary and concerning.
But that being said, we do need to consider that Deepin OS is still open-source software. As such, just like QuidsUp, anyone can audit the source code to find out if there are any backdoors in the operating system. And as far as we know, there hasn’t been any news or substantial evidence on this matter.
However, it is also worth considering that auditing the source code of an entire operating system is no easy task. It requires enormous time and manpower. As such, many security experts and Linux users argue that the distro hasn’t gone through enough scrutiny to know whether it’s “really” safe and secure.
Deepin Linux and its EULA
After its acquisition by Union Tech, the next release for Deepin OS was version 20. Since then, users are required to agree to the Deepin EULA (End User Licensing Agreement) & Privacy Policy before installing the operating system.
On one hand, it’s a good thing that Deepin is legally disclosing what’s going on in their operating system. But on the other hand, this makes Deepin one of the few Linux distros that require users to agree to a EULA, similar to proprietary OSes like Windows.
Now whether or not you like your Linux distro coming with a EULA is a different question. Let’s focus on what’s actually important – what does the EULA & Privacy Policy say? Does Deepin collect user data?
Well, it turns out yes – as a matter of fact, yes it does.
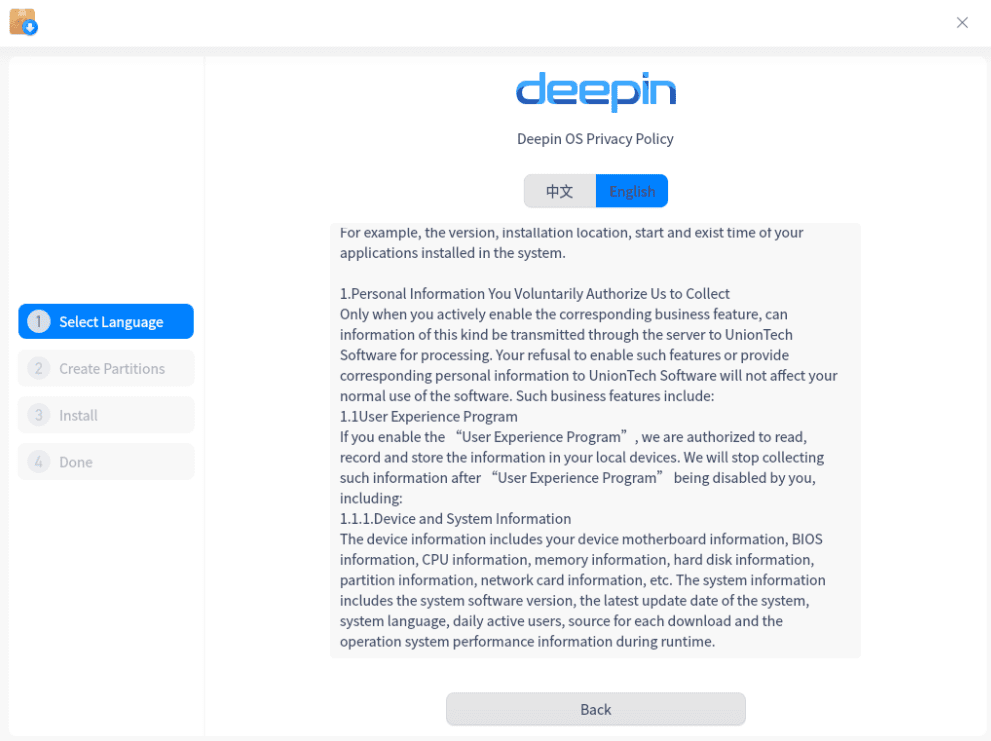
Deepin OS privacy policy
However, users have the option to opt-in or opt-out from providing Union Tech with their data.
So what kind of data does Deepin OS collect anyway? Well, here’s the complete list for you to go through:
- Network information e.g. IP Address
- Motherboard Information
- BIOS Information
- CPU Information
- Memory Information
- Hard Disk Information
- Partition Information
- Network Card Information
- System Software Version
- Latest Update Date for the System
- System Language
- System Sound Effects
- Power Supply
- Mouse
- System Theme
- Wallpaper
- Launcher
- Dock
- Configuration Information for Hot Corners
- Daily Login Time
- Source of Each Download
- The version of Installed Applications
- Start and Exit Time of Application
That’s a lot, isn’t it? And some of this doesn’t make sense for an operating system to collect. So, why does Deepin need to know about the “daily login time” for my system?
Now yes, as we stated, all of this tracking only happens if the users opt-in. But the very fact that this sort of tracking feature is present in the operating system is concerning for many users, and rightfully so!
So, should I use Deepin Linux?
Currently, there is no concrete or genuine proof that Deepin Linux is spyware. However, there’s no denying the fact that it has a bunch of red flags.
Deepin OS is now owned by Union Tech which is associated with the Chinese government, and this can be concerning for some users. Secondly, the operating system has many user data tracking features in place. Even though they are opt-in, the very fact that Deepin is going this route is understandably offputting to many Linux users.
As such, just to keep our readers (especially beginners who don’t know how to audit source code or detect unusual network traffic) on the safe side, we recommend skipping Deepin OS. With that being said, before you get all sad and depressed that you won’t be able to use this beautiful Linux distro, consider that we are critiquing the Deepin Linux distro and not the Deepin Desktop Environment (or DDE for short).
You can use the Deepin desktop environment! It is safe, and it’s not spyware!
If you want the good looks of Deepin without worrying about potential security and privacy issues, then you can just use the Deepin Desktop Environment on top of your favorite Linux distribution.
In fact, there’s a community edition of Manjaro on DDE as well as Ubuntu using DDE.
The CNZZ tracking script was embedded in the Deepin Store, which is a part of Deepin OS. If you are using the DEE on some other distro, you will most likely access the DDE Store. This is community-made, the code is available to everyone to audit, and it is not known to have any tracking scripts. So you are clear here!
Furthermore, if you install DDE on another distro, you don’t have to worry about the annoying Deepin EULA. We discussed all those tracking features as a part of the core Deepin OS and not integrated into the desktop environment.
Finally, if you are getting the Manjaro or Ubuntu spin-off DDE, then you can rest assure that their respective communities have thoroughly audited the source code of the desktop environment. After all, established distros don’t want to compromise their users as well as their name and goodwill by recommending spyware under their brand name.
Wrapping up
So this covers the entire Deepin Linux spyware controversy – the past and the present.
As we just said, there’s no substantial proof or findings that point to Deepin secretly collecting user data. And although the OS does have a system for tracking and collecting user data, you have the option to opt-in or opt-out, so it’s in your control.
But with that being said, the previous 2018 CNZZ incident, and the fact that Deepin is currently owned by Union Tech, which is partially under the Chinese government, are causing concern among a lot of users.
As such, if you are new to Linux, and you don’t know how to run security audits or track your network traffic, then we suggest that you don’t use Deepin OS. Instead, if you like how the distro looks, you can just install the Deepin Desktop Environment (DDE) on your favorite distro, and enjoy the UI/UX that way.
Both Manjaro and Ubuntu have DDE flavors that you can try out right now.


11 comments
How about the ‘Source of Each Download’? That sounds like it’s for the user in China. My biggest problem with Deepin is the localization. I’m not a Chinese speaker. I got popups in Chinese. So what did I agree to? I don’t know. Much of the app store is in Chinese also.
The UI may look nice, but I found the usability questionable. The system settings panels get in the way all the time.
A lot of Deepin apps is non-free. (Why?). You can not audit its source codes. https://mirror.redrock.team/deepin/pool/non-free/d/
Known security vulnerabilities are not fixed for a long time. Why?
https://bugzilla.opensuse.org/show_bug.cgi?id=1070943
https://bugzilla.opensuse.org/show_bug.cgi?id=1134131
https://bugzilla.opensuse.org/show_bug.cgi?id=1134132
https://bugzilla.opensuse.org/show_bug.cgi?id=1130388
What information are collected – there is a lots o it !!!
https://www.deepin.org/en/agreement/privacy/
I did not even realize I had opted in to “data collection”. Deepin 20.07 I just clicked in the usual manner to get on with the install. It appeared like a requirment. Certainly it was very shiny as advertised once installed.
Thanks for the heads up.
I tried the Deepin V23 alpha iso. Installed on a USB key. Installator asked for my language (French) but did not asked for the keyboard layout (fr-CA). So at first run I was stuck with an azerty keyboard instead of a qwerty and it was impossible to login. After each login error it blocks you for more longer … I had to boot on my regular distro and chroot in deepin to change the keyboard, reset the user blocking count and add a new user with an easy password just to be safe. In the /home there is the “linlong” user that is used to solve packages problem between rpm/deb. But this user is allowed to log in bash on the machine … And I don’t control the password of it … There is definitely many big security problem with this distro and we can’t really check what info it leaks to the chinese servers. I would definitely no touch the DISTRO even with a 10 foot pole.
Good try but sorry Mr Xi Jinping … don’t count on me.
There’s a reason why this version has the word “alpha” in its name. Instead of ranting about the problems here , how about actually making a report on bbs.deepin.org ? Frankly UnionTech are not as rich as Canonical, they can’t employ people to test every locale of the OS, they wouldn’t know of a French keyboard bug until a French-speaking user reports to them!
Reminder: DEEPIN ALPHA NOT TO BE USED IN PRODUCTION OR DAILY DRIVEN! We’ve said this so many times on our website.
As a Deepin contributor, I can assure you that v23 Alpha allows shell login for the linglong user temporarily, to help us debug the linglong package manager. Graphical and shell logins for linglong will be disabled in the release version of Deepin 23.
It’s a shame that ignorant people assume everything coming out of China is some “government approved spyware”…
Absolutely, spot on! It’s a shame when certain geopolitical concerns overshadow the essence of technology. Deepin’s open-source nature allows for transparency and scrutiny, regardless of its country of origin. It’s imperative to assess software based on its technical merits rather than succumbing to preconceived biases. Let’s redirect our efforts towards constructive contributions and collaborative endeavours to enhance the technology landscape.
Moreover, it’s essential to acknowledge that privacy concerns extend beyond borders. While some may point fingers at certain countries, it’s crucial to recognize that privacy violations occur worldwide. Platforms like Google, often celebrated for their innovation, have faced scrutiny for their data collection practices. It’s essential to hold all entities accountable for protecting user privacy and promoting ethical practices in technology.
Is Google a Spyware? I think all systems collect data.
Yes, Google is absolutely spyware!
Any reasonable, informed person will be wary of using a distro coming from any company partly owned by the communist Chinese government. That’s not ignorance. That’s not any shame on someone asking about a Linux distribution with such a tainted history and questionable origins. Not shame – it is due diligence.
The article has been edited on September 13, 2022, but it does not update the fact that the user experience program has been removed. It points out that the sheer amount of code is impossible to scrutinise, but then it suggests it’s alright to use DDE that apparently has been inspected by community remixes. I can’t help but feel that the article was written with malice. For example it points out that deepin has an EULA and automatically compares it to windows, while at the same time most corporation backed distributions (like Ubuntu) have some kind of eula too.